| Public and operator surfaces |
Canvas, community, admin, mobile, desktop |
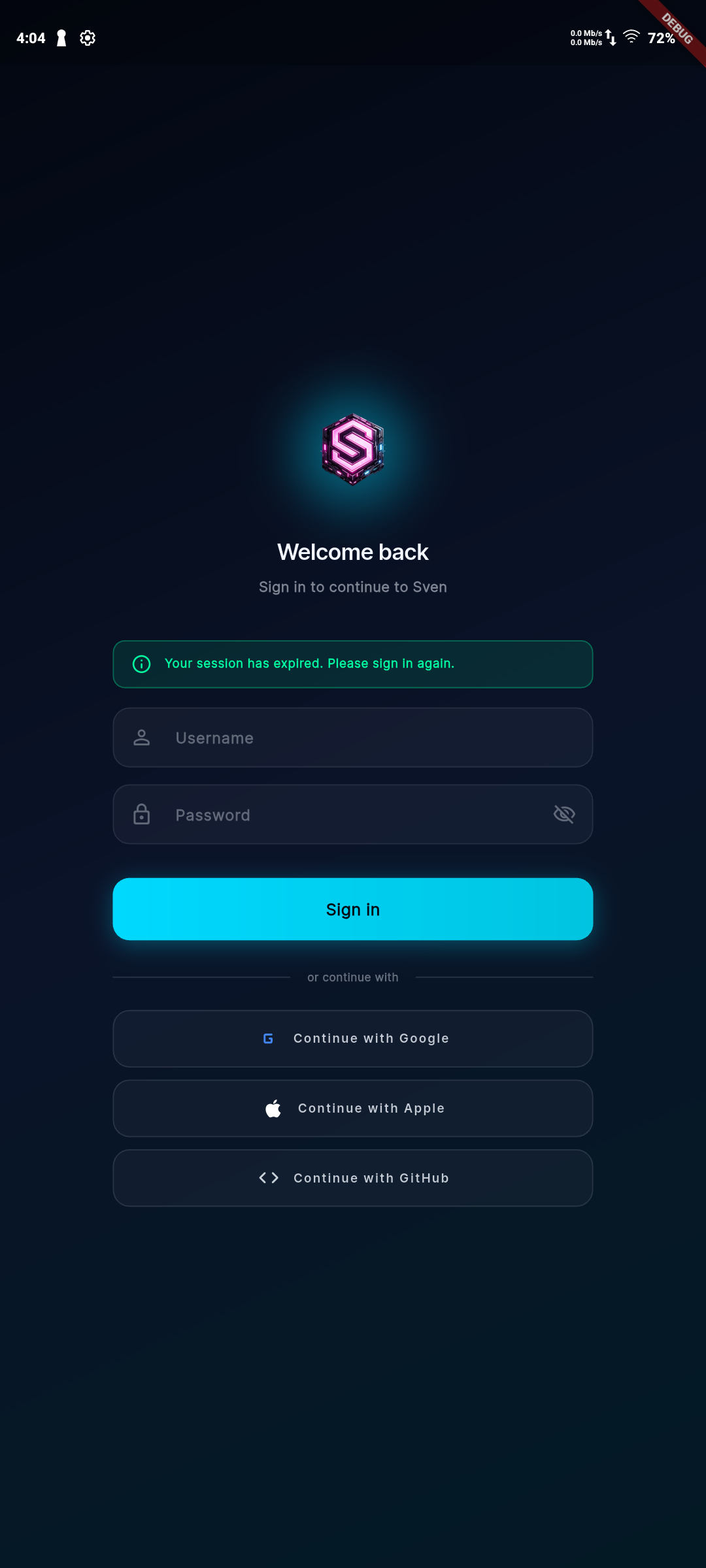
Route ownership and auth boundaries |
Users and operators get clear, purpose-built entry points |
| Knowledge and memory |
Persistent memory with retrieval and evidence trails |
Scoped access, provenance, and release checks |
Context stays useful without becoming opaque or unsafe |
| Voice and channel reach |
Local voice stack plus broad messaging coverage |
Adapter configuration and runtime health checks |
People can use Sven in the channels they already trust |
| Self-hosted deployment |
Installers, source-bootstrap paths, and production docs |
Release runbooks and environment-specific guidance |
You can run the platform on infra you control |
| Access and governance |
RBAC, SSO/OIDC, admin controls, reviewable actions |
Policy checks, audit trails, and gated release lanes |
Operational trust scales with the surface area |
| Proof and status |
Capability, community, and readiness endpoints |
Generated artifacts and CI-backed evidence |
Public claims can be checked against current status |
| Extensibility |
Skills, workflows, adapters, and multi-surface clients |
Contracts, docs, and operational controls |
The platform can expand without turning into a black box |
| Release readiness |
Status refresh, soak, drills, and signoff lanes |
Lifecycle validation and evidence retention |
Shipping quality is treated as part of the product |